How secure is email?
There’s no denying that email has been the best communication tool since facsimile, which conveniently replaced pigeons back in the day. It’s the default comms channel for most businesses – it’s easy, predictable and ubiquitous. But can it be trusted as a secure communication tool?
At the risk of sounding like a politician adverse to giving a straight answer…well, it depends. While there are ways to harden email security (mentioned in this article below), email is not recommended for exchanging confidential information.
Why are emails inherently insecure?
No end-to-end encryption
End-to-end encryption refers to the gold standard of messaging security where only the sender and their recipients can read the data – that is, your email is securely encrypted from the moment it leaves your device until it’s decoded on your recipient’s device (i.e. no third parties can access the data, not even your email providers). While popular instant messaging apps such as WhatsApp, Signal and Telegram offer end-to-end encryption, major email providers such as Gmail and Outlook do not by default. That said, Google had announced plans to roll out client-side encryption for Gmail, however, at the time of writing this article, this feature was only available to Google Workspace Enterprise Plus, Education Plus, and Education Standard customers.
So, is email encrypted at all?
Whilst by default your email may not have end-to-end encryption, that’s not to say there’s no encryption, but it gets complicated.
Firstly, let’s consider the journey of a standard email. Every time you click the send button, your email (and its attachments) traverses the internet across multiple servers before it reaches its destination. At each hop between servers, it’s at the mercy of server admin gals and guys, who in theory may alter or even delete your email content.
Now, most email providers do support a form of encryption whilst your email is in transit called Transport Layer Security (TLS). However, this assumes email providers (on both the sender and recipient’s end) have TLS enabled. Further, whilst TLS offers protection in the event your email gets intercepted by bad actors, your email providers themselves will have access to your email messages so that they can scan for malicious content. Prior to 2017, Google scanned emails for ad targeting, so thankfully this practice has stopped!
Phishing scams
Ahh, the pesky phishing attacks. At times these types of scams can be hilariously stupid, but they can also be incredibly sophisticated in their use of social engineering techniques to manipulate individuals into compromising their security by giving away sensitive information.
Often in phishing scams, the sender appears to be from a known source (such as a work colleague) and the email content is consistent with recent events (such as a recent purchase or transaction) – making them remarkably difficult to detect as they appear legitimate. Typically, the goal of the scammer is to convince their victim into clicking to a fake website to then enter confidential information such as login credentials.
Malware attacks
Malware attacks are also a type of phishing scam, but here the scammers have one very specific objective – and that’s to convince their victims to click on a link that then downloads malicious software onto their device. Once the malware is installed, it will then attempt to steal confidential information stored on your now-infected device.
Mistyping email addresses
Yes, we all take that extra bit of care when typing email addresses for the first time. But we’re all human and we make mistakes. When in a rush, it’s easy to mistype an email address resulting in your email landing in the wrong inbox.
The dreaded ‘Reply All’ blunder

We’ve all been there. You’re sweating bullets because you just had an ‘oh $hit’ moment realizing you forgot to drop some of the recipients cc’d in the thread and instead replied to all.
Recalling an email is not always possible
Depending on your email service provider, you might be able to recall or undo your sent emails. Now for the bad news, typically you only have a very limited time period to recall an email after hitting send, plus you can’t recall an email that has been opened.
If your email provider is Gmail, by default you have up to 5 seconds to recall, but this can be extended to up to 30 seconds in your Settings menu. For Outlook users, you have up to 120 minutes to initiate recalls – quite a handy grace period, now just pray your recipients have not already opened your email.
Securely exchange information with Portalstack's client portal solution
14-day free trial. No credit card required.
Top tips to securing your emails
Tip # 1 - Disable forwarding
Email being a broadcast form of communication, whenever you send out an email blast you’re sending information into the abyss in a sense – as you have little control over how that information is handled from the other end, your recipients.
That said, an example of what you may control is disabling the ability for your recipients to forward your email.
How to disable email forwarding in Gmail
- Click on the Toggle confidential mode button located in the bottom toolbar.

- Select your Set Expiration date. As described, this determines how long your email sits in the recipient’s inbox before it disappears.
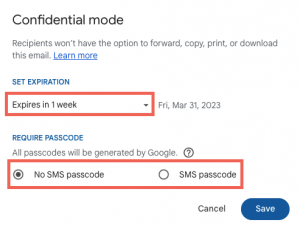
- Select if you require recipients to enter a passcode delivered to their phone via SMS.
If you select No SMS passcode and your recipient is a Gmail user then they’ll be able to open the email directly – for non-Gmail users, they’ll receive the passcode via email.
If you select SMS passcode, then you’ll be asked to enter the phone numbers for all recipients.
How to disable email forwarding in Outlook
Unfortunately, for Outlook users it’s a bit more convoluted. To disable email forwarding in Outlook you either need:
- Office 365 Enterprise license, or
- Install a S/MIME encryption certificate (out of scope for this article, but for those interested here are the installation instructions from Microsoft).
Assuming you meet either of the above, you can disable email forwarding by:
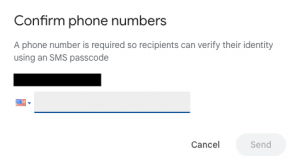
- Going to the Options menu
- Selecting the Encrypt icon
- Selecting the Do Not Forward option
Tip # 2 - Add two-factor authentication

For the cost of a small inconvenience, you could add an extra layer of security by adding two-factor authentication (aka 2FA) to your email account.
Once you’ve enabled 2FA, in order to access your email account you must enter two forms of authentication – your customary email address and password (first factor), plus a one-time passcode that’s either sent to your phone by SMS or an authenticator app (second factor).
For obvious reasons, 2FA makes it harder for hackers to gain access to your email account, even if they somehow gained possession of your password.
How to enable 2FA in Gmail
1. Sign in to your Gmail account.
2. Click on your profile picture in the top right corner of the screen and select Manage your Google Account.
3. Click on Security in the left-hand menu
4. Scroll down to How you sign in to Google, click on 2-Step Verification then follow the on-screen steps
How to enable 2FA in Outlook
To enable two-factor authentication in Outlook, follow these steps:
1. Sign in to your Outlook account.
2. Click on your profile picture in the top right corner of the screen and select My Microsoft Account.
3. Click on the Security tab from the menu
4. Click on the Two-step verification option then follow the on-screen steps
Tip # 3 - Use a password management tool
We all have this dilemma – we recognize having a strong password is important, but generating complex passwords and then remembering them is a legit barrier.
Thankfully, there are password management solutions out there that can:
- Auto-generate complex and unique passwords for each of your email accounts.
- Auto-reset passwords after a specified time period.
- Offer browser extensions to allow for easy access to your passwords.
- Share your passwords.
- Enable two-factor authentication from a single place.
Here are some popular password management solutions to consider:
Tip # 4 - Follow email best practices
Don’t send confidential information – bank details or any data that’s personally identifiable information.
Security awareness training – If you have a large(ish) team, perhaps consider mandating security awareness training for new employees as part of onboarding. Yes, no one ever gets excited over security training, but they’ll eventually get over it.
Alternatives to email that's more secure
If you do need to send confidential information here are some alternatives to email.
Private messaging apps

Private messaging apps are great for sending private information as most of them have end-to-end encryption that’s secured for text messages, as well as voice and video calls.
Here are some popular private messaging apps:
Encrypt messages with PGP
For sending super sensitive data (such as login credentials), you could use PGP (stands for Pretty Good Privacy, not a typo) to encrypt messages. This method does, however, require a bit of work for both you and your recipients.
Here is a great article on how to send encrypted messages using PGP.
Cloud storage providers
An alternative to sharing files and documents as attachments in email is to use cloud storage providers. It does require an extra process for your recipients to retrieve the files, but on the other hand, some of the benefits of cloud storage include:
- Secure storage space that’s encrypted whilst at rest (locked in a database and not in transit).
- Stored files are easily accessible.
- Better backup and redundancy.
- You can scale up or down storage space depending on your demand.
Here are some popular cloud storage providers to consider:
Portastack client portal is a great alternative to email, as it provides a more secure method for exchanging information with clients. You control who has access to what information, all behind a secure portal. It also means everything is conveniently organized in one place for your clients.
Share this article

